Updated April 2026 | Originally published on June 2024
The New York Department of Financial Services (NYDFS) is a regulatory body responsible for overseeing financial services and products in New York State. Its jurisdiction falls over financial institutions such as banks, insurance companies, and other financial services firms.
Compliance with the NYDFS Cyber Security Regulation applies even to businesses operating outside New York. It may extend to any organization that conducts business with entities regulated by the NYDFS. Financial services firms with operations, customers, or third-party relationships in New York also need to be aware of potential compliance requirements.
The November 2023 Amendment to NYDFS Section 500.7
Section 500.7(a) — The Universal Mandate
Every covered entity must execute on strict least privilege and access principles:
- Principle of Least Privilege: Limiting user and privileged access to Nonpublic Information (NPI) strictly to what is necessary for a specific job function. No more "just in case" access.
- Just-in-Time (JIT) Access: Privileged accounts must only be active when a task actually requires that level of access. Standing admin access is now officially a compliance liability.
- Continuous Review & Termination: Mandating annual reviews of privileges (at a minimum) and the prompt, immediate revocation of access when employees depart.
Section 500.7(b) — Password Policies
For all covered entities, if passwords are used as an authentication method, there must be a written policy meeting industry standards (referencing NIST SP 800-63B). This means implementing minimum length requirements, breach-checking, and strict no-reuse policies, while moving away from outdated mandatory complexity rotations.
Section 500.7(c) — Class A Company Mandates
For larger entities (over 2,000 employees or >$1B global revenue), the rules escalate significantly. Class A companies must:
- Implement a Formal PAM Solution: Policies are no longer enough; a dedicated, actual technology control for Privileged Access Management is explicitly required.
- Execute Continuous Monitoring: Organizations must log, alert, and continuously review what privileged accounts are doing.
- Automate Password Blocking: Systems must be capable of automatically blocking commonly used passwords across all accounts.
Meet NYDFS and CSA CCM requirements with Britive’s Unified PAM
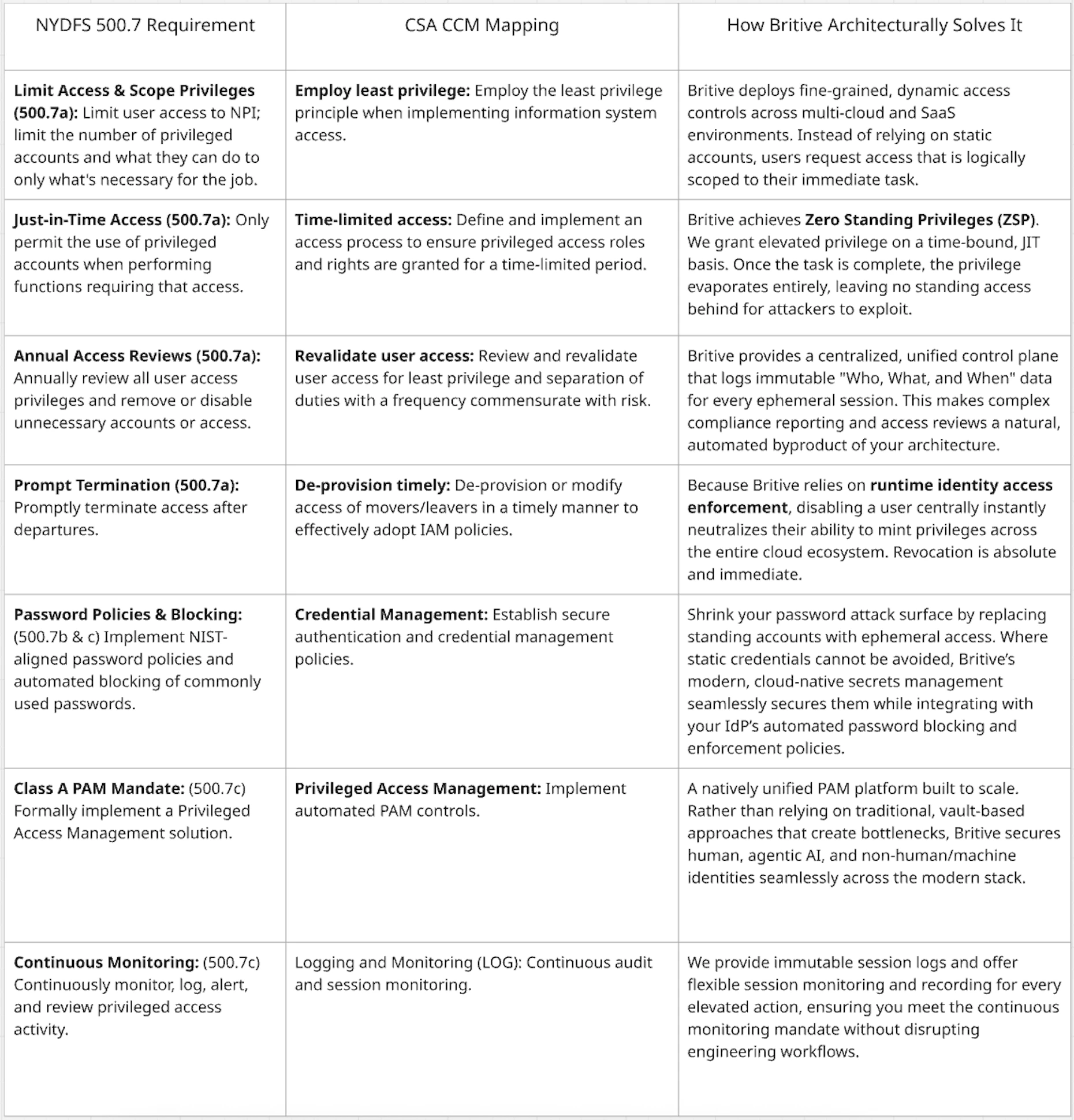
The Cloud Security Alliance (CSA) Cloud Controls Matrix (CCM) is a cybersecurity control framework designed specifically for cloud computing. It assists organizations in assessing risk and the requirements from NYDFS Section 500.7 can be mapped directly to it.
For modern financial organizations, especially those navigating the agentic AI conversation and the exponential scale of cloud environments, traditional vault-based PAM approaches often create operational friction. They also rely on standing privileges that exist 24/7, leaving unnecessary exposure in the environment.
Britive’s natively unified PAM platform fulfills the NYDFS 500.7 “implementation of a PAM” requirement, without the bottlenecks that accompany traditional approaches. By minting dynamic, ephemeral privileges at the exact moment of need, we provide true runtime identity access enforcement.
Here's how NYDFS requirements, CSA CCM standards, and Britive's architecture and approach align:
By November 1, 2025, NYDFS also requires MFA for anyone accessing an information system (Section 500.12). But layering MFA on top of standing privileges is only half the battle.
To truly protect your organization and seamlessly pass NYDFS audits, you must eliminate the standing risk entirely. Don't build your compliance strategy around storing static credentials. Build it around dynamic enforcement.